The cybersecurity landscape is rapidly evolving as we head into 2025, driven by the increasing sophistication of cyber threats and the growing importance of digital assets. Organisations are shifting their focus from traditional infrastructure security to data-centric measures, prioritising encryption, and robust data governance to protect sensitive information.
The rise of AI-powered tools, such as Microsoft Copilot and ChatGPT, presents both opportunities and challenges, as they can enhance security but also be misused by cybercriminals. As cyber threats become more complex and targeted, a proactive approach to threat detection and response, leveraging advanced analytics and AI, will be essential.
Looking at 2025 cybersecurity trends, this is what I anticipate:
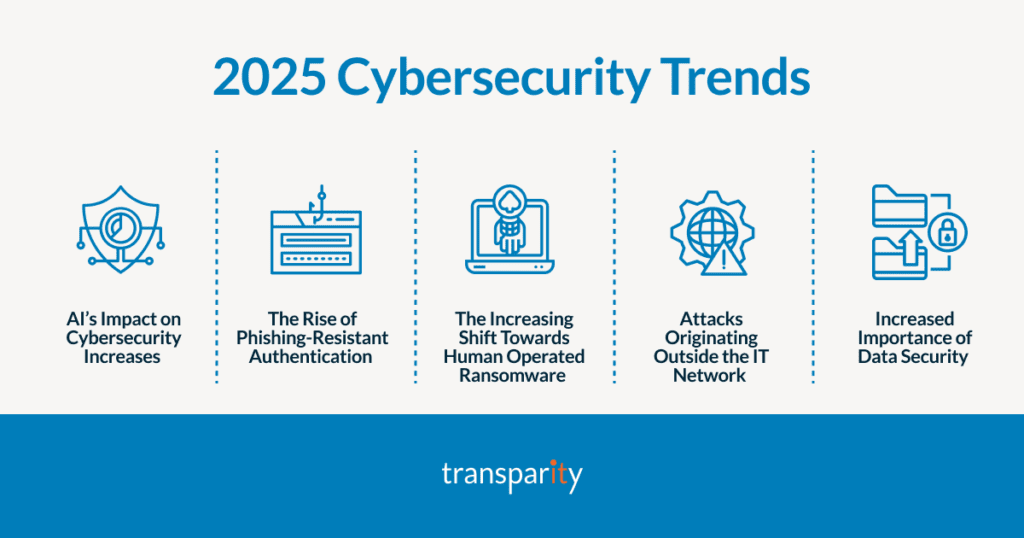
In 2025, AI will dramatically transform the cybersecurity landscape for both attackers and defenders.
For defenders, AI will enable real-time threat detection and automated responses, significantly reducing the time it takes to mitigate potential breaches. Machine learning algorithms will analyse vast amounts of data to identify patterns and anomalies, allowing organisations to predict and prevent attacks by identifying vulnerabilities and suggesting proactive measures. This will enable defenders to stay one step ahead of cybercriminals and protect their digital assets more effectively.
Conversely, attackers will also leverage AI to enhance their capabilities. AI-driven malware will adapt and evolve to bypass traditional security measures, while AI-powered phishing attacks will craft highly personalised and convincing messages to deceive targets. Additionally, AI will be used to identify and exploit vulnerabilities in systems more quickly than ever before.
This will create a constant arms race between attackers and defenders, with both sides continuously developing new AI-driven techniques to outsmart each other. As AI continues to advance, the cybersecurity landscape will become increasingly complex and dynamic, requiring constant vigilance and innovation from defenders to stay ahead of emerging threats.
Adversary-in-the-Middle (AiTM) attacks are expected to become increasingly sophisticated and prevalent. These attacks, which involve intercepting and manipulating communications between two parties without their knowledge, use highly convincing phishing kits that can deceive even the most vigilant users. These kits will include localised content and target fingerprinting, making them more effective at tricking individuals into divulging sensitive information. As a result, organisations will need to adopt more robust security protocols and continuously educate their employees about the evolving threat landscape.
Phishing-resistant authentication is becoming increasingly important as cyber threats evolve. Traditional multi-factor authentication (MFA) methods are susceptible to phishing attacks where attackers trick users into providing their authentication codes. To combat this, more secure methods must be implemented.
One such method is the use of phish-resistant passkeys. These passkeys are FIDO2 certified and provide resistance to phishing through two main mechanisms: proximity to the login device and the use of public key cryptography. This ensures that the authentication request is cryptographically verified, making it much harder for attackers to intercept and manipulate the process.
This year, human-operated ransomware attacks will become more sophisticated and targeted, posing significant challenges for cybersecurity. Skilled attackers will manually infiltrate networks, adapt their tactics in real-time, and deploy ransomware with precision, making it harder for traditional security measures to detect and prevent these attacks.
These attacks will focus on high-value targets like critical infrastructure and financial institutions, using a combination of social engineering, credential theft, and vulnerability exploitation.
Furthermore, increased collaboration between cybercriminal groups will lead to more coordinated ransomware campaigns. This trend will necessitate a more collaborative approach to cybersecurity, with organisations, governments, and security vendors working together to share threat intelligence and develop strategies to combat human-operated ransomware.
Expect a significant rise in attacks originating outside traditional IT networks. Cybercriminals will increasingly target operational technology (OT) environments, such as industrial control systems and critical infrastructure, exploiting vulnerabilities to disrupt operations and cause physical damage. The growing connectivity of OT systems to the internet will necessitate stronger security measures and continuous monitoring.
Internet of Things (IoT) devices will also become prime targets due to their often-weak security features. Attacks on IoT devices can lead to data breaches and unauthorised access. Organisations will need to implement comprehensive security strategies, including regular updates, strong authentication, and network segmentation to protect these devices.
Supply chain attacks will remain a significant threat, with cybercriminals targeting third-party vendors to gain access to their clients’ networks. Enhancing supply chain security through thorough risk assessments, stringent security requirements for vendors, and continuous monitoring will be crucial.
As organisations shift focus from infrastructure security to data security, they’ll prioritise data-centric measures like encryption and tokenisation to protect sensitive information even if infrastructure is compromised.
Data governance and compliance will become even more crucial as AI tools such as Copilot and ChatGPT become integral to business operations. Organisations must implement stringent data management practices to prevent unauthorised access and data breaches. This includes regular audits, strong authentication, and the adoption of privacy-by-design principles. Additionally, educating employees about the risks associated with AI misuse and promoting responsible use of these tools will be essential in maintaining a secure environment.
2025 cybersecurity trends are marked by rapid technological advancements and increasingly sophisticated threats. As cybercriminals continue to evolve their tactics, it is crucial for organisations to stay vigilant and proactive in their defence strategies.
Continued investment in security defences, including advanced threat detection, AI-powered tools, and robust data protection measures, are essential to safeguard digital assets and maintain trust with customers and stakeholders.

By prioritising cybersecurity and fostering a culture of continuous learning and innovation, organisations can better navigate the complex and ever-changing threat landscape, ensuring resilience and security in the digital age.
Cyber security threats continue to be a major concern for enterprise organisations everywhere – and they are growing more frequent and complex in nature. With hundreds of millions of new strains of malware emerging each year, IT departments devote significant resources to keeping their people and infrastructure protected.
In 2018 alone, there were 10.5 billion malware attacks. Increasingly intelligent and sophisticated, many of this new breed of malicious threats are able to hide from traditional anti-virus software – or even carry out their attack on systems without using any files at all in the process. Instead, they focus on entire networks or applications, and so are therefore far harder to detect.
What’s more, insider attacks from employees themselves are on the rise. As most activity mirrors that of legitimate users and is carried out on familiar devices like mobile phones and IoT infrastructure, they are also difficult to spot.
All of this means that technology solutions, tools and techniques around security have to constantly innovate and evolve just to keep pace. This is hugely challenging and puts great strain on hard-working IT admins.
However, help is at hand.
Machine learning (ML) has emerged at the very cutting edge of technology to protect organisations from these dangerous cyber threats. Using algorithms created from existing data, coupled with advanced predictive and statistical analysis, ML makes qualified assumptions about a device’s behaviour and actions – and then assesses how best to respond, based on that knowledge.
ML algorithms save security teams valuable time by identifying and analysing incidents and threats, providing visibility, accuracy and even a recommendation for action that simply isn’t possible by humans. To achieve this, these algorithms typically perform one of three mathematical tasks:
Regression: identifying correlations between different datasets, then understanding how and to what degree they are related to each other.
Classification: ‘training’ to recognise certain behaviours based on previous observations and learnings, then applying this to new data to predict future behaviour.
Clustering: working on new data and actions, but without factoring in any previous experiences or activities.
By leveraging ML’s considerable capabilities, Artificial intelligence (AI) plays a key role in helping to detect and mitigate security threats before they impact. Critically, AI is able to process far larger data volumes, at a far faster rate than any human can. Along the way, it flags any unusual or suspicious patterns of behaviour and other anomalies for investigation.
Typically created as tools within ML itself, AI uses a cause-and-effect approach (if X happens, assume Y will be the result) to construct predictable patterns of behaviour – which it then uses to judge the actions of people and devices using an organisation’s network. In this way, it vastly improves the speed, quality and effectiveness of cyber security in responding to and thwarting threats.
Good AI is typically:
Resilient: it can identify abnormal activity and prevent manipulation, coercion or other suspicious or unacceptable behaviour
Discreet: it is responsible, trustworthy and protective with all information it has access to
Transparent and accountable: it can act for you, and make educated and impactful decisions
To make the most of ML and AI, forward-thinking organisations are also now configuring a dedicated Security Information and Event Management (SIEM) solution within their operations. In essence, a SIEM gathers all available security-related data and events in one place, then correlates and analyses it with the purpose of improving responses to incidents and threats.
ML, AI and a SIEM are therefore vital building blocks for effective cybersecurity – and can make all the difference in mitigating network threats, automating application security, monitoring email activity and providing robust, next-generation anti-virus protection.
Microsoft’s security suite gives you the tools and intelligence you need to stay protected, efficiently and effectively – with less hassle for your IT team. You can enjoy the combined benefits of an advanced solution including:
Microsoft Sentinel is a scalable, cloud-native solution that provides SIEM, while managing and automating security tasks for swift response – together with accurate analytics and proactive threat intelligence – across all your users, devices, applications, and infrastructure, on-premises and in the cloud.
The Microsoft Defender suite offers comprehensive prevention against security breaches, which manages detection, prevention, investigation, and response across all your endpoints, identities, email, and applications. As a result, your IT admins can understand and learn from threats, their likely impact and how to mitigate them going forward.
A dedicated solution to stop breaches across your organisation by securing its various clouds and platforms while using integrated security tools to enable a rapid response to mitigate threats.
A Microsoft partner and complementary tool for Microsoft’s suite which uses ML and AI to monitor user behaviour, highlight any suspicious or unusual activity and monitor it for potential risk.
There is plenty of evidence for their success.
Back in 2018, advanced cyber criminals used trojan malware to try and install
malicious cryptocurrency miners on hundreds of thousands of computers across the world. Enter Microsoft Windows Defender, which used multiple layers of machine learning to identify and block perceived threats. The crypto miners were stopped before they could do any damage – in fact, almost as soon as they started.
Meanwhile, French insurance and financial services company AXA IT puts its trust in Darktrace cyber security to identify and manage online threats. Here, machine learning is used to scan for network vulnerabilities and automate responses.
However, success depends not only on installing on the stand-alone technical solutions – but also on ensuring they are properly configured to deliver the best results.
Our security team are experts in securing and maintaining modern work environments with best practice and best-in-class solutions. Our Managed Security Service brings together the combined power of Microsoft’s offerings to mitigate threats while removing the hassle of maintaining a secure environment at work through our monitoring, management and updates. Meanwhile, our Threat & Vulnerability Assessment gives you an accurate picture of the security of your environment and specific areas for improvement.
As a type of malicious software used by cybercriminals, ransomware destroys or prevents a person or business from accessing certain sensitive data or critical systems, until a ransom has been paid to the party initiating the attack.
Ransomware is particularly dangerous and disruptive – as it typically involves data or devices being suddenly locked and unavailable, without warning. Attacks occur either as social-engineered ransomware: which uses phishing where the attacker poses as a legitimate company or website to trick a victim into clicking a link or opening an email attachment; or as human-operated ransomware: where an attacker steals account information to gain access to an organisation’s IT network, then targets information and systems which they can infiltrate.
Once breached, the attacker installs the ransomware so that their targets become inaccessible to those who own them. For example, they might encrypt files or lock data. The victim is then asked to pay a considerable sum of money to get their access back (often in cryptocurrency). In the majority of cases, they oblige – to avoid the potentially devastating consequences to reputation and operations. Sadly, paying does not necessarily guarantee a happy ending.
Businesses around the world are increasingly being impacted by more frequent and sophisticated ransomware attacks. Indeed, The European Union Agency for Cybersecurity (ENISA) recently reported that between May 2021 and June 2022, approximately 10 terabytes of data were stolen every month as a result of ransomware threats. Almost 60% of the files stolen contained personal data relating to employees.
Microsoft has also confirmed “a massive growth trajectory for ransomware and extortion”. In 2021 alone, ransomware attacks shot up by 935%.
Prominent examples have included the Human Resources giant Kronos, which suffered an attack in December 2021 compromising its client cloud payroll and time-off systems; U.S. fuel pipeline Colonial Pipeline, which was shut down in May 2021 after a ransomware attack exposed the personal information of thousands of employees – resulting in soaring gas prices across the American East Coast and costing the company $4.4 million; and German chemical distribution company Brenntag, which has its network breached in April 2021 through stolen credentials which exposed the birthdates, Social Security numbers and driver’s license details of more than 6,000 individuals, as well as some medical data. This also ended up costing $4.4 million.
Inevitably, strengthening and maintaining your organisation’s security posture will help protect you from these significant threats. What’s more, you’ll actually save money in the long run – by avoiding costly remediation and even worse, the possibility of having to pay cybercriminals.
Microsoft’s extensive security suite provides you with everything you need to stay confident and protected. Here are a few important steps you can take to make this happen.
By focusing on removing any potential security vulnerabilities in your IT infrastructure, you can thereby make it harder for opportunists to breach it. For example, Multifactor Authentication (MFA) is a proven and easy way to protect your employees’ devices.
It sounds obvious, but the most effective way to stop ransomware is by installing a solution that directly combats it. Effective antimalware can detect and mitigate threats – for example, Microsoft Sentinel, Microsoft 365 Defender, or Microsoft Defender for Cloud.
By ensuring that all your employees stay up to speed on the latest threats and how to spot them, you can ensure that everyone across your organisation adopts a best practice approach to IT security and protection – which makes a big difference.
Cloud-based services such as Azure Cloud Backup Service, Azure Block Blob Storage Backup, or Office 365 Backup and Recovery Services create a safer environment for you to store and retrieve sensitive data. Plus, if this information is compromised, it makes it faster and easier for you to recover it.
65% of organisations haven’t implemented Zero Trust. Zero Trust consists of three pillars; explicit verification, least privilege and assume breach. Evaluate all your devices and the access requirements of employees, before allowing them access to corporate applications, files, databases, and other assets. That way, you are making it much less likely for a malicious identity or device to breach your systems and install ransomware.
Make sure you promptly install system updates and software patches as they become available.
If you are faced with a ransomware breach, it’s critical to be prepared. Take time now to plan out your course of action and the specific steps you will take to mitigate different attacks, so you can minimise any impact and get operations back to normal as quickly as possible if the worst occurs.
Depending on the severity of the ransom requested, you might be tempted to pay it there and then to solve the issue and stop the disruption. But although that seems logical, unfortunately you’re dealing with criminals – who may have no intention of keeping their word and may never give you back the access to your data. Indeed, most ransomware security experts advise against paying attackers anything, for this reason; not to mention that you would be funding illegal activity by doing so.
Instead, focus on what you can do personally as individuals and an organisation, to reduce the damage done by the incident. Where possible, isolate any data that has been compromised as quickly as you can, to stop ransomware spreading. Run your antimalware across everything – and ensure it’s updated to protect against any further attacks. And report everything to the police, to help them track activity and take action.
Transparity has extensive experience in creating and maintaining strategies to keep your business secure and prevent ransomware from compromising it.
We are experts in securing and maintaining modern work environments. Our advanced Managed Security Service helps you to mitigate threats while minimising the efforts and hassle of IT security operations: while our dedicated Threat & Vulnerability Assessment offers an accurate overview of your IT environment status and highlights specific areas for security improvement.
Take advantage of our Microsoft-funded workshops to enjoy in-depth guidance on these topics and improve your security posture. Explore Microsoft’s extensive security toolset, analyse current threats and create a strategic security plan to protect and govern your organisation’s data.
Hybrid working has been evolving gradually in businesses over recent years – but the Covid-19 pandemic suddenly accelerated its adoption. Organisations of all sizes and in all locations were forced to start working remotely, almost overnight.
Although this has enabled many excited and unprecedented opportunities for employers and employees alike, it has also created new and extreme challenges for IT security teams tasked with managing this brave new working world.
What’s more, with working practices changing so quickly, increasingly sophisticated and devious cybercriminals are exploiting any vulnerabilities exposed along the way to take full advantage. One-third of all employees have experienced harmful cyber activity; one in five have been victims of identity theft1. The average cost of a ransomware breach now stands at some $4.62m – which does not even include the cost of the ransom itself – and the average cost of a breach increased by 10% between 2020 and 2021 alone.
Worryingly, it takes an average of 287 days to identify and contain a data breach, start to finish. To put this in perspective, a breach on January 1 will take until October 14th to solve. That means serious and lasting, even permanent, business disruption.
Clearly, the risk of breach is greater than ever. So, protecting sensitive data and information is paramount.
Despite this, there is no doubt that hybrid working is here to stay. As such, cybercrime will continue to spread as employees work more disparately in different countries and continents, on a variety of devices. Organisations now have a large and urgent responsibility to empower and enable this modern working environment, by providing flexible, secure technology anytime, anywhere.
Acknowledged by leading global security bodies as the gold standard in cybersecurity, the
Zero Trust philosophy demands that an organisation must reliably verify any person or thing asking to connect to its technology systems, before allowing them access.
Undoubtedly, those organisations with a Zero Trust process in place are better protected against potential attacks – and better placed to respond swiftly and successfully when they happen. Threats are spotted and stopped faster, and life is made easier for hard-working IT teams thanks to performance analytics and insights.
The commercial case for Zero Trust is compelling. The average cost of a breach for organisations without a Zero Trust security posture in place is $5.04 million; for those in the mature stage of zero trust deployment, this cost falls to $3.28 million. Put simply, the sooner Zero Trust is in place, the safer and more resilient your business will be. Studies show that the average organisation saves $20 per employee per month by eliminating now-redundant security solutions in favour of the Zero Trust framework. In turn, the volume of security and IAM-related help desk calls fall by 50% – and security teams themselves are also 50% more efficient, while the associated risk of a data breach is halved.
Security decision-makers confirm that developing a Zero Trust strategy is their number one priority, with no less than 96% stating that it’s critical for success.
So, we’ve established that implementing Zero Trust is a no-brainer – and the good news is, it’s easy to get started. But what exactly does Zero Trust mean, and what does it consist of?
The framework itself is made up of three core elements: Zero Trust (to never trust anyone and always ask them to verify their identity); Least Privilege (once verified, to only provide them access to the things they absolutely need, and only for the minimum amount of time required); and Assume Breach (to always assume that any protection will fail, through either user error or system fault).
Rather than assuming that your corporate network and systems are safe and protected by your existing security solution, Zero Trust assumes the opposite: that there is a constant threat trying to make its way in and disrupt operations. As such, it asks all users, endpoints, networks and other resources to verify their identity explicitly at all times.
This works on the principle of only providing users with access to the things they specifically need to do their work, for the specific time they need them. This same rule goes for applications, systems or devices. In this way, the potential for cybercrime is significantly reduced because the accessible environment becomes a fraction of what it was previously.
No cybersecurity strategy is infallible, so assume breach always prepares for the unexpected. This means stress-testing an organisation’s cybersecurity ecosystem by developing and evolving processes on the assumption that a breach has already happened – or soon will.
These concepts are simple to deliver at speed, given the right approach. For example, multi-factor authentication provides excellent protection by making employees confirm their individual identities by using something they have, such as a hardware token or SMS message, and a second authentication method, before they are permitted to access any files or resources. Moving to this type of password-less authentication does require some planning and warning; however, once in place it significantly strengthens security while also delivering a superior user experience for those involved.
Similarly, Single Sign-On (SSO) boosts security while simplifying authentication by removing the need to manage multiple credentials and reducing the number of sign-in prompts needed to access working materials.
Three-quarters of organisations have started implementing a Zero Trust strategy, with over one in three claiming they have a strategy fully up and running. For them to remain successful, managing employee cultural challenges with regard to security and protection will be vital, as will sustained support from leadership teams.
As part of our fully managed security service, Transparity’s comprehensive Zero Trust framework delivers gold-standard IT security, across your organisation.
Enjoy end-to-end protection, managed by experts who constantly monitor and improve your security posture, based on the latest performance metrics and observations. As a result, you’re always perfectly prepared to respond to and remediate any threat or incident, before it impacts your operations.
To assess how far your organisation is on its Zero Trust journey, talk to us. We can help identify your current maturity, plan your security roadmap, and keep you secure from day one.
1 Source: Annual Cybersecurity Behaviors and Attitudes Report 2021 – National Cybersecurity Alliance
As the comprehensive and end-to-end system for producing and distributing a given product or service, a supply chain runs all the way from the very first stage of sourcing required raw materials, right up to final delivery of the product or service to its customers and clients.
As such, it plays a critical role in ensuring the commercial success of organisations – and involves a myriad of teams including producers, vendors, warehouse and logistics personnel, transportation companies, distribution centres, retailers, and so on.
Although supply chains are typically associated with manufacturing companies and processes, in fact all organisations operate some kind of supply chain – from financial services to law firms. As such, these organisations all rely on a number of suppliers to deliver and manage their elements smoothly, in order to conduct their own business operations effectively.
Because it performs such an essential and holistic role, effective supply chain management can make a big difference to operational efficiency and overall profitability. That said, it also acts as a backbone – and if one element breaks down, the rest of the chain can quickly be disrupted too.
Maintaining a coherent, connected supply chain is more challenging than ever. As technology evolves and business models go global, operations are becoming incredibly complex and intricate to manage. There are more potential failure points and higher levels of risk. Thousands of suppliers might contribute to a single product or service, from places all over the world. Even the most robust processes can struggle to keep up – and that’s where vulnerabilities begin.
The kinds of attacks suffered by a particular industry will have a lot to do with what kind of infrastructure they rely on, what kind of data they handle, and how people (customers, employees and everyone else) interact with them.
Recent years have seen a significant increase in the number of cyber-attacks resulting from such supply chain vulnerabilities. These attacks can have potentially catastrophic consequences for the organisations involved – and they’re the reason why supply chain leaders highlight five key security concerns in their work:
Despite these concerns, recent research in the DCMS 2022 Security Breaches Survey found that only just over one in ten businesses review risks posed by their immediate suppliers (13%) – and only 7% do it for their wider supply chain. This is something that must urgently change if industry is to combat the ever-changing world of cyberthreats. Social engineering and ransomware attacks are both on the rise, with manufacturing now one of the most targeted industries according to Microsoft’s Digital Defence Report.
Many supply chain professionals still remember the major data breaches suffered by large retailers like Target and Home Depot, arising from compromised third-party relationships.
During the pandemic, the SolarWinds breach sent shockwaves across the industry and triggered a much larger supply chain incident that affected thousands of organisations, including the U.S. government. It was one of the largest ever recorded and compromised the data, networks and systems of thousands of people. More than 18,000 SolarWinds customers installed the malicious updates, with the malware spreading undetected and then even more malware was installed to spy on other companies and organisations. More recently, Toyota was forced to shut down all 14 of its Japanese factories after an attack on part of its supply chain.
The average cost of a data breach now stands at $3.86 million, with mega breaches (50 million+ records stolen) reaching $392 million… and these figures will only keep rising.
How can you protect your own supply chain against these serious and complex threats?
It’s best to adopt a multi-pronged strategy – by taking a number of different actions.
First, evaluate where you are today. Assess your existing security governance, for data privacy, third-party risk, and IT regulatory compliance. Identify any weaknesses and gaps, and think about what ‘safe’ looks like – where you want your business to be.
Running vulnerability scans and fixing highlighted issues acts as a quick fix to plaster over any obvious immediate risks. This won’t affect your business operations too much and can make a big difference to your overall security posture, with minimal effort.
Strategically, look to digitise your core manual processes wherever possible. By moving away from repetitive, paper-based processes which are prone to human error and not managed by technology, you will improve security and reliability regarding your data and the way it moves between employees and clients.
Any data protection policies you introduce should include discovery and classification tools to encrypt databases and files with sensitive customer information, financial data and proprietary records, to ensure these stay private and secure. Identity and access management security should also be introduced for anyone sharing or handling this data.
Planning proactively preparing for a breach or disruption is also vital. Assume that the worst may happen – and have an effective response in place.
Without doubt, the best IT security strategy to deliver the above protection is one based on three pillars of cybersecurity: Zero Trust, Least Privilege and Assume Breach.
Zero Trust stipulates that no one should ever be automatically trusted – and always asked to verify their identity. Least Privilege asserts that once verified, they should only be given access to the things they absolutely need, for the minimum amount of time required. Assume Breach adopts the mindset that any protection will eventually fail, so we should always be ready to respond.
The Zero Trust philosophy is recognised by 96% of security professionals as critical to their organisation’s success.
Our Managed Security Service is built on the core principles of Zero Trust and informed by the latest threat intelligence – so you can always be confident you’re one step ahead of emerging risks.
Our experts work proactively to close vulnerabilities and continuously improve your security posture with 24/7 support, whenever you need it. We also offer Microsoft-funded workshops so you can benefit from specific, in-depth guidance from our security experts and get actionable steps and insights you need to improve your security posture.
The internet of Things – or IoT – describes an ecosystem of connected computing devices and entities. They include machines, objects, and people, each with their own unique identity, exchanging data across a network.
We see many examples of these entities in our everyday lives, wherever technology is at work. In cars that use sensors to alert us when maintenance is required for a particular area – like tyre pressure or oil top-up; in household appliances like refrigerators and ovens that let us know when food needs restocking, meals are ready or thermostats are adjusting; in people with medical modifications like heart monitors or pacemakers; and so on. IoT is all around us, and constantly evolving.
All these things constantly collect, send and share data they generate from their individual environments and interactions. In this way, software can analyse how each thing is behaving and make improvements in real-time for the greater good – to enhance quality of life, increase efficiency and productivity, ensure safety, reduce costs, and many other valuable benefits: all with hardly any human intervention.
Undoubtedly, IoT helps people get more from their personal and professional lives. It is also creating exciting new possibilities for businesses of all sizes, through operational insights, intelligence and automation. 68% of executives believe that adding new IoT devices
to their environments is critical to innovation and growth.
However, its widespread usage and vast access to and management of data makes it a high-profile target for hackers. 60% of security practitioners believe IoT and OT environments are one of the least secure parts of their IT infrastructure – and 39% of organisations have recently experienced a security incident where an IoT device was the target of the attack.
If IoT systems are not properly protected, the consequences may be devastating.
All these billions of devices and data points represent an enormous attack surface for cybercriminals. As connected device volumes increase and more information is shared, the potential to steal and exploit confidential or sensitive information also increases.
What’s more, the nature of IoT means that if a single, harmful piece of malware enters the ecosystem, it will quickly spread between devices – and could avoid detection for a long time. This is about more than personal data. An IoT breach could threaten critical infrastructure, including electricity, transportation, healthcare and financial services. It’s also extremely disruptive to, and expensive for, operations. A recent ESG report, Analyzing the Economic Benefits of Microsoft Defender for IoT cited that the average downtime resulting from each attack is 21 days – and that avoiding a ransomware attack can save a company with 32,500 devices more than $35 million over three years.
Securing your IoT is therefore essential – and it starts with Zero Trust.
Firstly, check that your overall business environment is protected and capable of keeping IoT devices safe. Verify your employees and ensure you have visibility of the devices they’re using on your network – to ensure they’re authorised to use them. Once you are happy that standard baseline security requirements are met, you can focus on the IoT aspect in more depth.
Register all relevant devices and use strong identity authentication so you can always be sure that they are talking to and being accessed by the right people. Implement Least Privilege access rules to mitigate any damage resulting from these identities and devices being compromised by a hacker. Assess the existing security posture and health of your IoT ecosystem, evaluate vulnerabilities and insecure passwords, then maintain ongoing threat monitoring. And upgrade and update your security continually so you can be confident you always have the best protection in place.
Microsoft’s suite of IoT security solutions provides you with this peace of mind, without compromising your working life. Benefit from visibility and status of all your IoT assets and devices while improving your security posture using a risk-prioritized approach that harnesses built-in AI, automation and hands-on expertise. Plus, if the worst should happen, you will be able to respond fast with tools that are specially optimized for your security operations centre.
Microsoft Defender for IoT discovers and displays assets the moment they are connected – so you can quickly and easily secure them. Networks segmentation offers additional security for your data and devices, while continuous monitoring means threats can be detected and fixed before any lasting damage is done to your business. In fact, Gartner gave Microsoft the highest rank for execution in its magic quadrant evaluations of endpoint protection platforms, on this basis.
To ensure a holistic approach, it’s best to involve an independent consultant: someone who can get to grips with your business and its needs yet offer impartial advice about how to achieve your objectives.
Transparity can help. Our security team are experts in securing and maintaining modern work environments and can implement best practice for your IoT ecosystem.
Using our advanced Managed Security Service, you can mitigate threats while removing the hassle of maintaining a secure environment at work through our monitoring, management and updates. Meanwhile, our Threat & Vulnerability Assessment gives you an accurate picture of the security of your environment and specific areas for improvement.
For many years, Operational Technology (OT) has managed and monitored the performance of individual devices for organisations across a wide range of industries, including manufacturing, transportation and utilities.
Because it sits at the very core of processes, OT has played a critical role in ensuring productivity, efficiency and compliance for businesses of all sizes – not to mention, the health and wellbeing of society at large.
OT is often the catalyst that enables goods to be manufactured in factories. Hospitals and healthcare providers rely on OT to maintain quality of patient diagnoses and treatment. In short, it acts as the oil in the engine for many of the products and services we all enjoy in our daily lives.
Traditionally, OT was used in industrial control systems for monitoring and adjusting physical equipment and machinery. Adjusting these devices was mechanical with closed, proprietary protocols rather than being networked.
OT was siloed, operated locally and in isolation from other technologies and locations. However, as technology has developed, they have become increasingly connected, opening up greater opportunities for remote control and more precise monitoring.
To bridge the disconnect, in recent years OT has converged with IT systems as part of the Internet of Things, to support organisations in meeting their increasing compliance demands and providing integrated data analysis across the board.
Linking IT systems to OT devices in this way makes business processes more intelligent and informative. Wireless connectivity enables administrators to monitor systems more accurately and control physical devices remotely. Data can then be analysed in real-time, so improvements can be made faster and more effectively.
For example, in a factory setting, a converged IT/OT system can analyse the entire manufacturing process end-to-end, to highlight any inefficiencies and potential areas for improvement – giving management the opportunity to take action and make operations more profitable. The same system can identify the optimal times for device maintenance to be carried out, to maximise lifespan and minimise downtime – all of which saves a significant amount of money.
But there is a downside. Having all these devices connected and collaborative leaves them vulnerable to all the same security breaches that threaten the rest of IT – financial loss, reputational damage, falling customer confidence and even jeopardised national security. Mitigating these risks are vital, not only to keep organisations safe, but also to keep critical infrastructure functioning.
These vulnerabilities are very real. 90% of organisations have experienced an OT security breach – 58% in the past 12 months – and more than three in four expect regulatory pressure to increase over the next two years.
For these reasons, almost everyone anticipates major challenges in moving towards converged IT and OT regarding security, including a lack of third-party and/or in-house expertise to support the convergence itself, and the potential leakage of sensitive or confidential data.
Siloed processes and teams can exacerbate these problems still further. Individual teams in an organisation often have different priorities, giving rise to different approaches and appreciation of risk within IT. When it comes to shared OT, therefore, this creates inconsistencies which can manifest as inefficiencies through wasted or duplicated effort and conflicting practices. Together with mounting concerns around privacy and compliance, this means there is a real need for a holistic approach that ensures OT governance and best practice on an organisation-wide basis.
Microsoft’s extensive security suite provides advanced, integrated protection against OT threats. Using the latest AI, Machine Learning and Microsoft Graph Security API and applying the principles of Zero Trust, regular vulnerability assessments and penetration testing, it offers your business cutting edge monitoring, detection, and response to thwart cybercriminals and keep your systems online.
Everything is included under one roof, as part of our 24/7 Managed Security Services.
To ensure a holistic approach, it’s best to involve an independent consultant: someone who can get to grips with your business and its needs yet offer impartial advice about how to achieve your objectives.
Transparity can help. Our security team are experts in securing and maintaining modern work environments and can implement best practice for your OT/IT environment.
Using our advanced Managed Security Service, you can mitigate threats while removing the hassle of maintaining a secure environment at work through our monitoring, management and updates. Meanwhile, our Threat & Vulnerability Assessment gives you an accurate picture of the security of your environment and specific areas for improvement.
Employees everywhere will by now be familiar with the concept of ‘Bring your own device’ (BYOD) technology – the policy of permitting people to configure and use their own PC and mobile devices for work purposes.
Indeed, more than 50% of organisations and over 70% of employees use personal devices in this way – and the numbers continue to grow. This evolution is relevant for everyone: 87% of businesses depend on their employees’ ability to access critical mobile business apps from their smartphone – and they gain some 240 hours of extra productivity work per year from these employees as a result of allowing them to work in this way.
Unsurprisingly, the recent pandemic only served to accelerate this trend, as companies increasingly moved employees to home working. This is expected to continue for at least the next five years. The BYOD market will hit $367 billion in 2022. As such, enabling and maintaining secure BYOD remains at the top of the agenda for IT security teams around the world.
It’s not hard to see why BYOD practices are so popular. After all, organisations enjoy a host of benefits. There is less hardware to buy – and the hardware that is needed can be a lower spec. Employees are happy, because they are free to use the devices they prefer in the way they want. They can also stay connected with teammates, wherever they’re working. Meanwhile, employers save money in the process. They don’t have to buy, upgrade or manage employee-owned devices – from computers and printers to smartphones, tablets and peripherals.
At first glance, BYOD seems like a win-win. However, as more people use their personal smartphones or laptops to work in this way, the security risks for organisations increase exponentially – for all sorts of reasons.
Personal devices are by nature less secure. This is because they are less stringently monitored and harder to control than business-owned ones. As such, cybercriminals are more likely to target them to break into corporate networks, as they can exploit security vulnerabilities more easily. This is a critical issue, as it leaves networks using BYOD potentially open to hacking, data loss, and even insider threats from employees themselves.
50% of companies allowing BYOD have experienced a data breach directly through a personal device – and almost half of data breaches (41%) happen on lost or stolen devices. Just 7% of the 70 million devices stolen each year are recovered. Despite this, surprisingly only 56% of BYOD companies use mobile device management (MDM) to maintain security on these types of devices.
While working on their own devices, employees can easily and inadvertently visit insecure sites and download dangerous malware and viruses. If these threats stay undetected, they can spread and infect the entire organisation – with serious and potentially long-lasting consequences.
Unless your employees have tightly secured sensitive content on their devices, hackers can breach their files and create issues for your business. What’s more, if the device is lost or stolen, malicious individuals may gain access to your company network.
As part of the above, enabling employees to use their own devices to access and manage critical business information like financial records, customer details and intellectual property can leave your organisation vulnerable if this information is exposed or compromised.
Being aware of these risks – and taking steps to mitigate them on an ongoing basis – is essential to safeguard your people, business and reputation.
So, what can you do to ensure strict governance and endpoint security for BYOD?
By ensuring everyone is up to speed on security best practice and the associated risks, you can go a long way to minimising breaches. Set out a clear and consistent BYOD security policy and make time to share it in detail with your people. Everyone should understand what they can and cannot do on their personal devices.
Make sure that personal and business data stay separated, to ensure appropriate security and privacy is in place for sensitive files and information which employees may not want to share in a workplace environment. Directions of how to do this should be included in your BYOD company policy.
Encourage employees to connect their devices to networks they know are protected and secure, wherever they are working. An encrypted virtual private network (VPN) will provide the safety they need to work productively without jeopardising any sensitive files and information.
Explore the option of creating virtualized desktops to give employees a dedicated, secure workspace on which to automatically store applications and files on shared drives. This enables IT to be managed centrally, in one place, so you can oversee activity and keep things protected and backed up. Look at enforcing MDM and endpoint security so that you are able to remotely wipe data from any lost or stolen employee devices.
We have extensive experience in creating and maintaining this type of best practice for BYOD and beyond.
Our security team are experts in securing and maintaining modern work environments. Using our advanced Managed Security Service, you can mitigate threats while removing the hassle of maintaining a secure environment at work. Meanwhile, our Threat & Vulnerability Assessment, powered by Tenable Nessus, gives you an accurate picture of the security of your environment with specific actionable next steps and areas for improvement.
Multifactor Authentication (MFA) is a fundamental element of any robust cybersecurity provision, and is used by more than 55% of enterprises. However, cybercriminals are always coming up with new ways to attack targets, by any means necessary, and have set their sights on breaking through MFA. This blog will cover MFA push bombing.
Multifactor Authentication (MFA) adds additional layers of verification to login attempts in addition to a password. MFA requires an individual to verify their identity in two or more ways before they can access resources like online accounts or a company VPN. Typically, MFA uses something you know (like a password or PIN), something you have (like a smartphone) or something you are (biometric data like fingerprints, facial or voice recognition).
MFA is an easy and effective way to improve your security. By adding another layer of verification you reduce the risk of attackers gaining access via weak or reused passwords, which can be traced back to 63% of data breaches.
MFA prompt or push bombing, otherwise known as MFA fatigue and MFA spamming is a method of social engineering attack where hackers send verification prompts to users until they approve the request. While that might sound like a simple enough method of infiltration to avoid, it’s proving to be effective against some large organisations.
LAPSUS$, a cybercrime group specializing in deploying ransomware against large companies in the UK and internationally, have successfully hacked major companies like Nvidia and Okta this year alone. According to this report, a member of the group described how effective MFA bombing can be on their official social media channel “Call the employee 100 times at 1 am while he is trying to sleep, and he will more than likely accept it. Once the employee accepts the initial call, you can access the MFA enrollment portal and enroll another device”.
Once the group infiltrated Nvidia’s network, they deployed ransomware to steal up to 1 terabyte of data. Then, the group threatened to release the data unless their demands were met.
MFA push bombing is a social engineering attack, meaning it takes advantage of the user’s behaviour in order to gain access. It’s not just bombarding users with notifications; it also involves less conspicuous methods to gain verification.
While waking someone up with notifications in the middle of the night might work for some, for others, an inconspicuous notification or two might be enough for a user to verify the request without raising alarm. Another method might be impersonating the company’s security or IT team and claiming the request is part of planned works or maintenance.
MFA push bombing is just one method attackers can use to get access to your systems. From there they can pursue their aims whether it’s to hold your data for ransom, collect and leak data or any number of other malicious activities. The cost of a breach spans financial, reputational and commercial damage. For example, the average cost of a ransomware breach for detecting and securing the breach and lost business is $4.62 million, and that doesn’t include the cost of the ransom itself which can be vast sums. In May 2021 it was reported that CNA Financial, one of the USA’s largest insurance companies, paid an astonishing $40 million to recover their data after a ransomware attack.
Cyberattacks happen more often than you’d think. MFA push bombing, fatigue or spamming is just one way attackers can use to gain access. According to the Federation of Small Businesses (FSB) there are approximately 10,000 attacks per day on just small businesses in the UK alone.
The best way to defend against this type of attack and other vulnerabilities is by implementing an end-to-end security solution with 24x7x365 protection and response. Cybercriminals will take advantage of any vulnerability they can find, including working out of hours in the hopes of catching targets off guard.
In addition to this, user training is vital to ensure your team don’t accidentally open the door to attack. As mentioned earlier, social engineering attacks rely on the vulnerabilities of users, like clicking on malicious links or phishing attacks. To overcome this risk factor, your security provision should include consistent user education and a Zero Trust mindset.
Our 24x7x365 fully Managed Security Service offers the best in cybersecurity protection. Traditional reactive security methods fail to protect your data and only respond once it’s too late and the damage is done.
Our security experts take a proactive approach, hunting out vulnerabilities and safeguarding your data from potential risk. We continuously enhance your security posture, so your environment remains resilient against new and established tactics. Informed by the latest threat intelligence, our experts stay steps ahead of highly motivated cybercriminals.
With expert support and defence around the clock, your environment is never left vulnerable to attack and we’re always on hand if you need us. Plus, we offer end-user training so every member of your team is a part of maintaining your security.
Some of the ways we keep you protected against MFA attacks include:
We have the experts and the industry experience to defend your environment and protect you from MFA attacks. Get in touch for a free Threat and Vulnerability Assessment to understand your current security posture, potential vulnerabilities and what services would be best for you. We’ll work to understand your priorities and challenges and partner with you to find the solutions that are right for you.
Passwords are part of the fabric of our lives. Every day, we enter our own personal combination of characters to access everything from emails, bank accounts and files to shopping, insurance and travel. Most of us are comfortable doing this and confident it will keep us protected – as long as we stay vigilant and remember to update our details from time to time.
However, unfortunately passwords are not as safe as you might think. Without additional security alongside them, they will not provide proper protection from cybercriminals.
Back in 2017, Google confirmed that hackers steal almost 250,000 web logins each week – and that number is likely to be even higher now. Breaches like this are not just inconvenient, they’re highly dangerous for both the individuals whose identities are compromised, and the businesses serving them.
Typically, when we are told about the importance of staying safe online, we tend to think it’s to protect our financial affairs. However, data breaches go far further and can impact our lives in all sorts of ways. For example, the healthcare sector is a common target for hackers who can alter patients’ medical records to gain money fraudulently from providers and insurers. It’s big business, and a big problem.
More recently, the global pandemic has accelerated the evolution to remote and hybrid working, which has increased these risks and left many organisations under-prepared to safeguard their disparate employees. The number of cybercrimes reported to the FBI quadrupled during the pandemic, and the same pattern was true across all industry sectors.
Successful hackers can cause mayhem quickly once they gain access to data and systems. They install malware, steal sensitive information and disrupt operations. Dealing with this can be painful – and extremely costly. IBM has confirmed that it takes 275 days on average to contain a data breach. That equates to some nine months without regular ‘business as usual’ resources. Ultimately, resolving all disruption can take as long as three years.
As such, businesses are making it a priority to address these risks – and more than 55% of enterprises have turned to Multifactor Authentication (MFA) to enhance their security.
Multifactor Authentication is a security measure that requires an individual to verify their identity in two or more ways before they can access resources like online accounts or a company VPN. Typically, these options ask for details about the person’s possessions, things that only they know (passwords or PINs) or unique biometric data such as fingerprints and voice recognition.
63% of data breaches can be traced to weak or reused passwords, so by adding an extra layer of authentication, Multifactor Authentication mitigates this from happening. MFA can also prevent more than 95% of bulk phishing attempts and over 75% of targeted attacks.
If you haven’t considered MFA yet, it’s time to start.
MFA is an attractive option because it’s easy to implement and makes it much harder for the average criminal to steal sensitive information. For remote workers using unsecured home or public networks, MFA safeguards their credentials and minimises the chance of hackers breaching their systems. And it’s remarkably effective. Microsoft confirms that MFA blocks nearly all attempted account hack attempts. This one tiny fact could enhance your corporate security across the board.
Here are three reasons you should start using MFA to protect your business, right now.
Because MFA only grants access when several conditions are satisfied, it mitigates the risk of a breach happening when someone’s password is compromised. In short, it adds another vital layer of security to keep persistent hackers at bay for longer, thereby avoiding potentially damaging attacks. Plus, because it uses personal devices or biometric data like fingerprints, it’s much harder for hackers to fake.
As organisations change and employees perform their roles in increasingly varied and disparate locations, MFA is an ideal solution to keep their sensitive data safe wherever they go. Adaptive MFA goes one step further, to accurately predict a person’s potential risk factor when they ask to access resources by assessing their device, location or other contextual details.
Passwords are essential to digital life – but they can be a pain. These days, they demand complicated combinations of upper- and lower-case letters, numerals, symbols and so on. The more different passwords we create, the less we’re likely to remember them all. In the end, the temptation is to take a ‘one-password-fits-all’ approach, which exposes our vulnerabilities.
MFA gets round this by giving you a platform to secure your corporate environment and every individual and device inside it. No time-consuming maintenance or constant resets. All of which frees up your IT team to work on other important priorities.
Transparity has the expertise and industry experience to put MFA to work for your business and ensure you stay even more secure. Our advanced threat intelligence and Managed Security Service have been specially developed to optimise our customers’ protection while also future proofing against emerging risks.
Contact us to arrange a free threat and vulnerability assessment to understand your current security posture – and how MFA can benefit you.
Modern manufacturing is more complex and connected than ever before. From Internet of Things (IoT) equipment to vast supply chains, manufacturers are increasingly vulnerable to security risks from external threats. One vulnerability that may go overlooked, is the threat of a cyberattack gaining access to systems and data via supply chain partners.
In the ever-changing world of cybersecurity, there is a growing trend of cyberattacks taking advantage of the explicit reliance on trust in the connections between businesses in the supply chain. In fact, 82% of data breaches in manufacturing come from external threats and 92% are motivated by financial gain.
Social engineering and ransomware attacks are both experiencing a marked increase, with manufacturing in the top 3 most targeted industries for ransomware according to Microsoft’s Digital Defence Report.
Supply chain attacks can be devastating for manufacturing businesses, disrupting operations and costing significant sums in damages. Recently, Toyota was forced to shut down all 14 of its Japanese factories after an attack on a member of its supply chain, resulting in the production loss of around 13,000 vehicles.
Cybersecurity is essential for businesses of all sizes to mitigate the risk of a cyberattack. The best defence is a robust security set up based on the three pillars of cybersecurity – Zero Trust, least privilege and assume breach.
These pillars make up the Zero Trust philosophy which is fundamental to a solid defence. In fact, 96% of security professionals see it as critical to their organisation’s success.
Microsoft’s extensive security suite has all the tools you need to maintain the security of your organisation. From Microsoft Sentinel for monitoring your environment to Microsoft Defender for Endpoint to secure users’ devices, Microsoft has the tools you need to keep your data secure end-to-end.
To manage the security risk from the supply chain, it’s important to understand the potential vulnerabilities each business may have. While manufacturers can’t control the cybersecurity of their partners, by understanding the level of protection they each have businesses can prepare for the most likely exploits.
Cybersecurity is a continuously evolving challenge, as cybercriminals develop new, more sophisticated ways to gain access to valuable data. To stay ahead of the threat, organisations need security experts at their side maintaining and perfecting their defences.
Our Managed Security Service is built on the core principles of Zero Trust, informed by the latest threat intelligence to stay ahead of emerging risks. Our experts work proactively to close vulnerabilities and continuously improve your security posture with 24×7 support, so you can be confident in your security.
Take advantage of Microsoft funded workshops for in-depth guidance from our security experts. Explore Microsoft’s extensive security toolset, analyse current threats and create a strategic security plan to protect and govern your organisation’s data. Get actionable next steps to improve your security posture and put your questions to our experts so you walk away with the insights you need.
With increasingly online, connected, and complex manufacturing methods comes the added risk of bad actors taking advantage of unforeseen vulnerabilities. While the risk is significant, it can be dramatically reduced through robust security measures and consistent security hygiene.
With an ever-evolving cybersecurity landscape and continually emerging cyber threats, it’s vital to stay steps ahead. Microsoft has announced the introduction of two new security products to bolster their existing suite, addressing threat intelligence and external attack surface management.
Here, we’ll cover everything you need to know about Microsoft’s new security tools – Defender Threat Intelligence and Defender External Attack Surface Management.
Microsoft Defender Threat Intelligence (Defender TI) brings together several functions of a SOC engineer’s threat intelligence and analysis workflow into one portal. This new portal assists a SOC analyst with studying the latest threat intelligence, threat analysis, CVE-ID, and incident response.
Microsoft’s core concept for this platform is Infrastructure chaining, this concept uses the relationships between highly connected datasets to help the SOC team build out a richer and more in-depth investigation into threats, both from alerts SOC analysts have seen in products such as Sentinel or through active threat hunting. This allows them to understand the bigger, so they can respond and keep your environment safe.
The portal is not a solo journey, it allows members of your Security team to gain insights from other Security teams’ actions to detect and prevent threats, so security experts around the world can collaborate to block out threat actors.
Microsoft Defender External Attack Surface Management (Defender EASM) is located in Azure and provides a SOC team with an understanding of the business’s external attack surface. Unlike the attack surface of an endpoint or firewall, the external attack surface includes data like registered domains, hosted web pages, SSL certificates, and hostnames.
Microsoft Defender EASM works by discovering observed connections on the internet using discovery seeds. Seeds are defined as legitimate assets, they discover and inventory any infrastructure that could belong to the environment or has a relationship with a legitimate asset. This means your SOC team are aware of the full extent of your external attack surface, not only what is within the firewall environment. The process is recursive over time it’ll pick up any new assets, and inventory them ready for the SOC team to assess.
Defender EASM not only inventories the external attack surface, it also provides vulnerability, compliance, and security posture dashboards to help your security team prioritise and protect your assets that would’ve otherwise been vulnerable to attack.
We’ll help you understand more about these new products and how they can support your security posture. Plus, our experts will work with you to detect and close any vulnerabilities in your environment with our industry-leading Threat and Vulnerability Assessment.
As the threat landscape continues to change minute by minute, we’re dedicated to keeping your environment secure and making your security posture stronger every day. Get in touch today.