The digital landscape is continuously evolving, prompting organisations to prioritise secure and efficient identity management systems. The rapid evolution, and occasional rebranding, of Microsoft’s Identity-as-a-Service (IDaaS) offerings can leave developers and architects a little confused.
This article covers a few of the options of Microsoft Identity Management Solutions.
Identity-as-a-service (IDaaS) refers to cloud-based solutions that provide identity and access management (IAM) functionalities. These services help organisations manage user identities, authenticate users, and control access to resources in a secure and scalable manner.
Microsoft introduced Active Directory as an Identity Management solution with Windows 2000 a quarter of a century ago, and after countless enhancements, it is now the standard for user authentication and management within organisations. AD offered enhanced security, scalability and improved integration, providing a single sign-on experience across multiple systems within an enterprise, reducing the number of passwords users needed to remember and simplifying the management for IT staff.
In 2008 Microsoft took AD into the cloud to create Azure Active Directory (now Entra ID).
Although designed primarily to manage users within a single Azure tenant, Entra ID does allow authentication of users from other directories through federation, guest users, or by registering multi-tenant apps with bespoke authorisation rules.
Without cluttering up your AD with large numbers of inactive guest users, the only option for securing public-facing web applications was once to create a bespoke identity solution. Microsoft introduced Azure AD B2C in 2015 to solve this problem, allowing an app developer to use multiple third-party identity platforms for authentication.
The idea of a third-party identity provider seems counter-intuitive but it’s not much different to the idea of passports. I have a passport issued by HM Passport Office; if I travel to the USA, I can use my passport for identification because the USA government trusts HM Passport Office. Similarly, if you are developing an app, you can decide which of a number identity providers that you want to trust, e.g. Google, Facebook. But, just as a UK passport won’t grant me entry to the USA without a visa granted by the USA government, a token from a third-party ID provider serves only as a means of identification and does not convey permissions – the owner of the tenant in which the app resides has full control over who is allowed in and what they are allowed to do once they’re in.
Although highly customisable, once you move past the limited number of out-of-the-box options available through the Azure portal, customisation becomes exponentially more complex. In our experience at Transparity, most implementations require custom policies, generated from lengthy hand-authored XML files. The lack of developer tools for customisation, the complexity of customisation, and ongoing management create a large technical overhead in many implementations.
Although still fully supported, Azure AD B2C is now considered by Microsoft to be a ”legacy solution”.
See how Arco partnered with Transparity for a Seamless Migration to Azure AD B2C
“We are thrilled with the seamless migration to Azure AD B2C, which has significantly improved our user authentication process. We appreciate the expertise and dedication shown throughout this project, making it a resounding success.”
In 2023 Microsoft addressed the known shortcomings of AD B2C with their newest IDaaS offering, Entra External ID. Built on a zero-trust architecture, External ID significantly simplifies the configuration process for administrators and developers and provides a more consistent experience for users. Hand editing of XML files is no longer required to create user flows, with Microsoft claiming that custom policies are no longer needed with External ID. In addition to a much improved administrator experience, External ID also has integrations for Visual Studio and Visual Studio Code to aid developer productivity.
Not many, but this is relatively new technology and there are a few idiosyncrasies that will no doubt be ironed out in time. The lack of custom policies, and current lack of policy migration tools, might eventually drive some developers back to using “legacy” AD B2C.
The availability of feature-rich IDaaS offerings means that there are now very few scenarios where you would need to build your own fully bespoke identity solution. However, if you needed that flexibility, then Microsoft Authentication Library (MSAL) makes it relatively simple to write .NET code to create and validate your own JSON web tokens (JWT), a core requirement of modern authentication solutions. This is the tip of the iceberg though. On top of the basic token creation and evaluation, just for an MVP you also need a secure and performant data store for your users’ data; governance to ensure compliance with relevant data protection laws; fully bespoke and secure user management functionality including sign-in, sign-up, profile editing, password reset; and the ability to monitor and review logins to detect suspicious activity.
This all amounts to a significant development and ongoing management overhead, and unless you are a very large organisation, a government, or a new social media platform, have a large team of developers at your disposal, and a substantial budget, this option should usually be avoided.
Read our blog to learn how to streamline Identity Management – The journey to Azure AD B2C
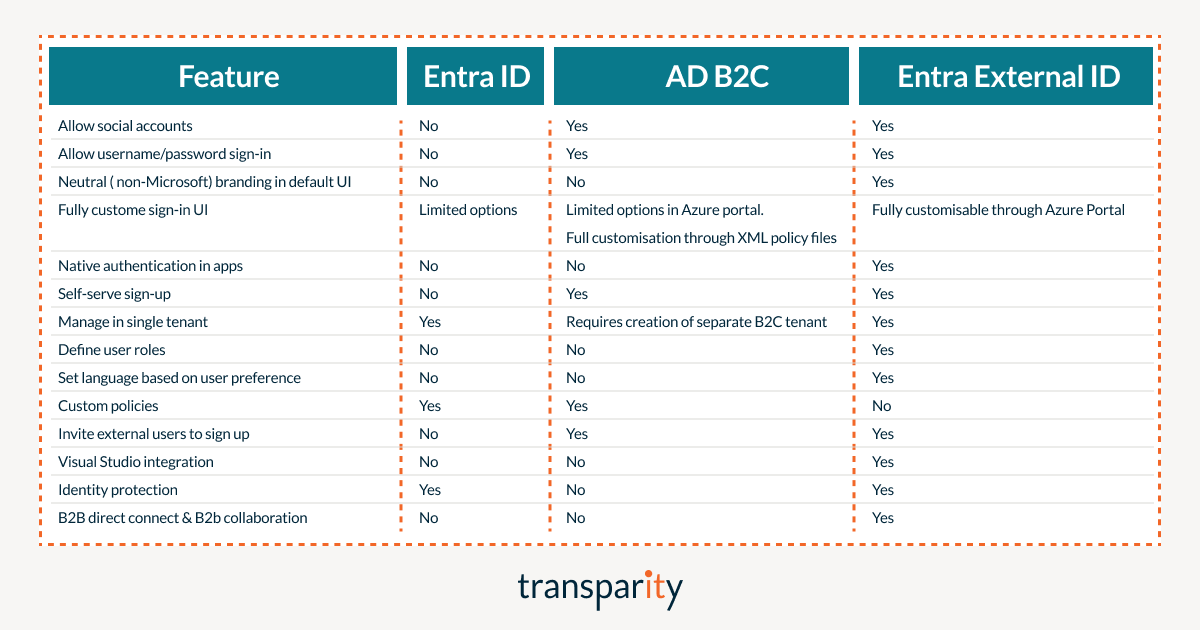
Common features of Entra ID, Entra External ID and Azure AD B2C:
This table shows some of the key differentiating features.
Whereas migrating legacy systems from Azure AD B2C to Entra External ID would seem like an obvious move, there is currently very little in the way of tools to migrate custom policies. We are led to believe that this is something Microsoft are working on. Currently Entra External ID would seem to be a better candidate for greenfield development and it might be prudent to wait a while before migrating existing systems using AD B2C.
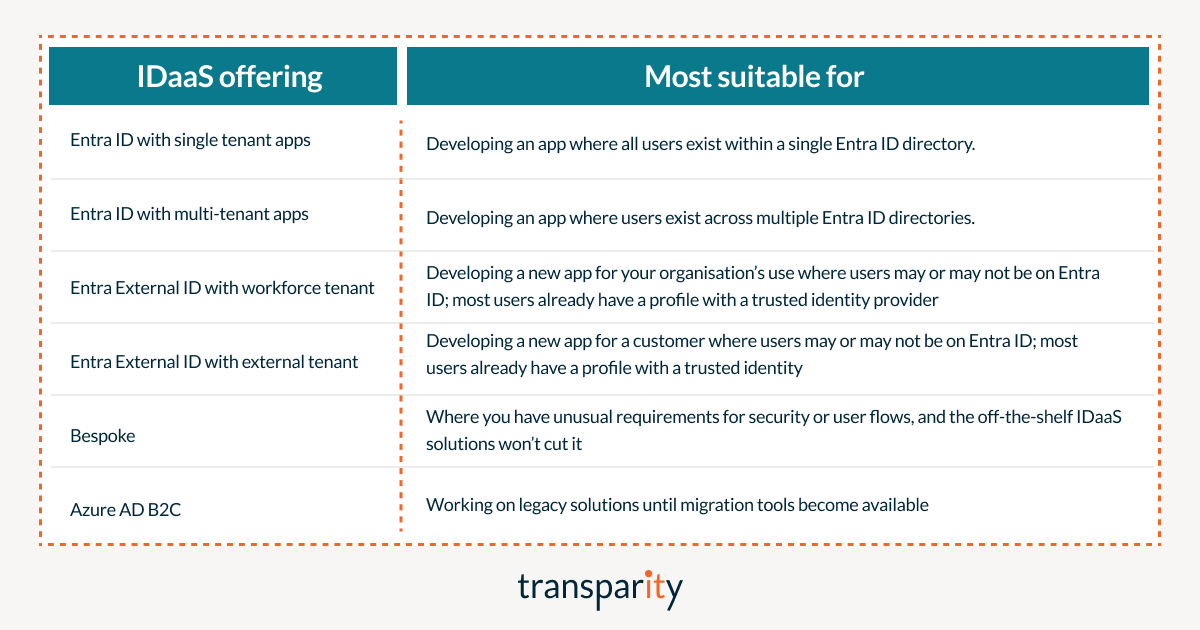
When deciding which Microsoft Identity Management solution to select for a new development, the following simple rules should help.